Protect the value that keeps life, business, and reputation in motion.
PROHTEK unifies risk architecture, cyber resilience, intelligence, executive protection, continuity planning, and productized monitoring into one premium defense platform for enterprises, private clients, and sensitive locations.
Security should preserve continuity, not just display force.
The platform is designed around the assets that drive value. That means protecting the person, the network, the location, the reputation, and the recovery path as one connected system.
Move from fragmented vendors to one coordinated protection architecture.
- Protect what creates value, not merely what is easiest to guard.
- Converge cyber, physical, legal, and operational response into one command logic.
- Measure protection by continuity, resilience, and avoided loss.

A premium service system structured around resilience and recovery.
Each pillar maps to a distinct stage of protection maturity, from valuation-led diagnostics to integrated defense and specialized intelligence operations.
Total Value Risk Mapping & Strategy
Strategic advisory designed to identify, rank, and harden the assets that drive enterprise continuity and personal resilience.
View pillarConverged Adversarial Defense
One operating model across physical security, executive protection, cyber defense, and operational resilience.
View pillarSpecialized Intelligence & Recovery
Threat intelligence, due diligence, digital forensics, and recovery operations that preserve continuity under pressure.
View pillarTwo inquiry-only products designed to turn protection into a repeatable operating edge.
Mammoth Shield hardens customer-facing browser presence. Global Eagle Eye broadens visibility across public locations and global assets. Both are positioned as controlled-access PROHTEK capabilities, not commodity tools.
Mammoth Shield
A browser-presence protection product that maps web exposure, watches for trust breaks, and shields customer journeys before attackers can separate users from the brand.
- Maps browser exposure across domains, sessions, and user journeys.
- Flags tampering, impersonation, malicious scripts, and trust-surface drift.
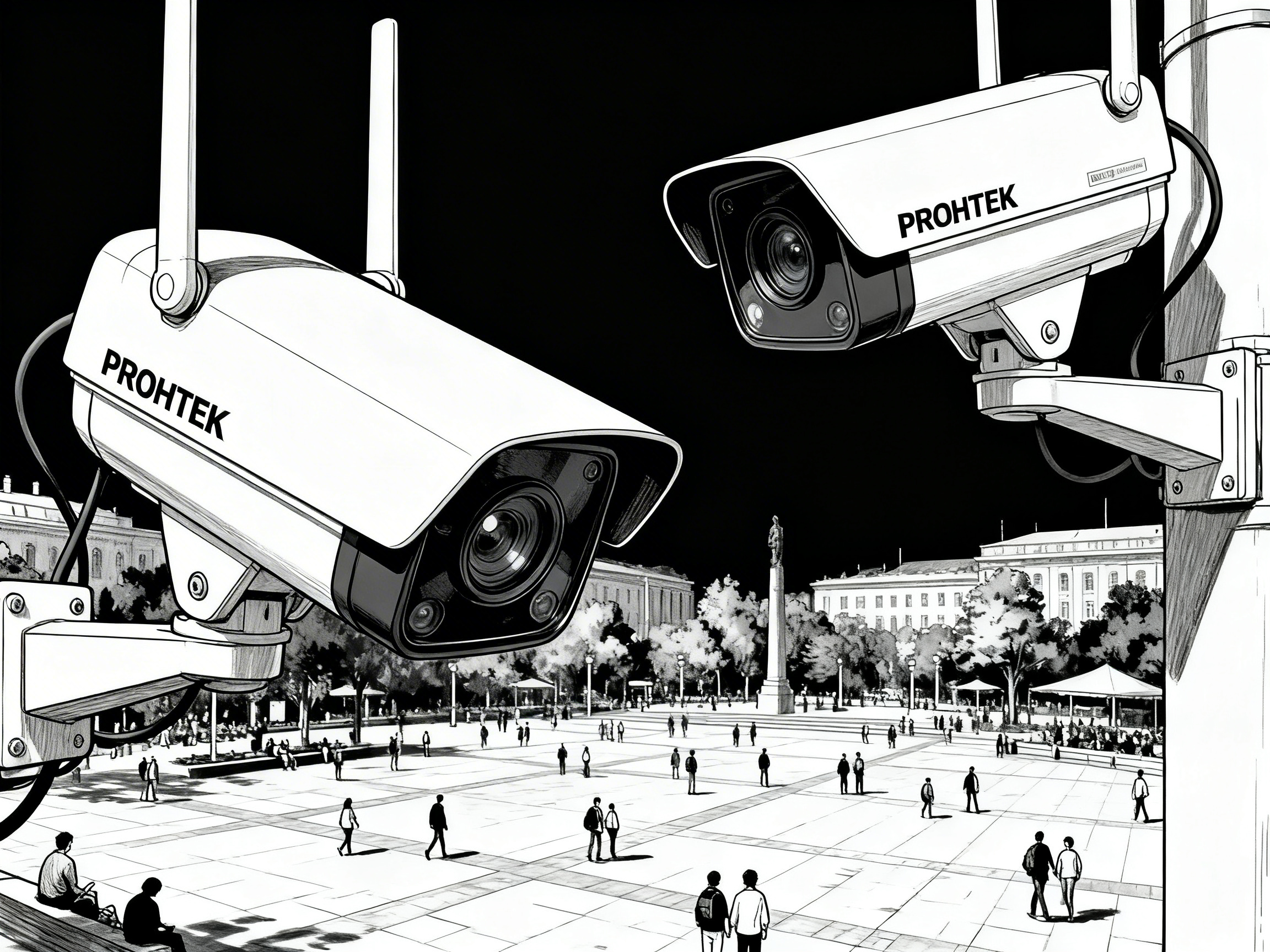
Global Eagle Eye
A browser-based awareness surface for global locations, public feeds, and critical movement corridors, curated for clients who need wide-angle visibility before decisions are made.
- Brings camera, transit, maritime, aviation, and public-space awareness into one view.
- Supports watchlists, regional scanning, and high-value location context.
High-value protection services that connect strategy to action.
Every service is designed to support concrete client outcomes: reduced exposure, faster decisions, stronger continuity, and cleaner recovery.
Enterprise Risk & Value Audit
A ranked map of physical, cyber, reputational, and financial loss vectors across the full client footprint.
- Identify the assets that matter most to continuity and valuation.
- Rank vulnerabilities by likely impact and exploitability.
Legal Entity Shielding & Audit
Review legal structures, trusts, holding entities, and operational exposure points that weaken asset protection.
- Surface structural legal vulnerabilities before a hostile event occurs.
- Coordinate entity, compliance, and operational risk logic.
Continuity Planning & Pre-Crisis Strategy
Continuity plans, tested playbooks, and recovery design to preserve operations and leadership confidence through disruption.
- Reduce unacceptable downtime across sites, teams, and vendors.
- Prebuild decision authority and escalation paths.
Unified Threat Management Stack
Integrated oversight of digital environments, surveillance systems, access controls, and operational telemetry.
- Faster escalation across cyber and physical indicators.
- Shared visibility across sites, networks, and vendor controls.
Executive & Digital Protection
Protect the executive, family, communications, digital identity, and public exposure as one connected asset.
- Reduce targeted exposure tied to digital footprint and travel.
- Coordinate personal, family, and communications protection.
Supply Chain & Operational Resilience
Assess vendors, partners, internal processes, and site dependencies that can turn into continuity or fraud events.
- Reduce vendor-driven cyber and operational exposure.
- Reveal weak controls before they trigger downstream loss.